In the realm of cybersecurity, the concept of the Pyramid of Pain has emerged as a critical framework for understand and palliate the impact of cyber threats. This model, developed by protection expert David Bianco, provides a structure approach to prioritise justificative strategies based on the level of effort and pain visit on adversaries. By rivet on the most impactful areas, organizations can enhance their protection stance and get it more difficult for attackers to achieve their goals.
Understanding the Pyramid of Pain
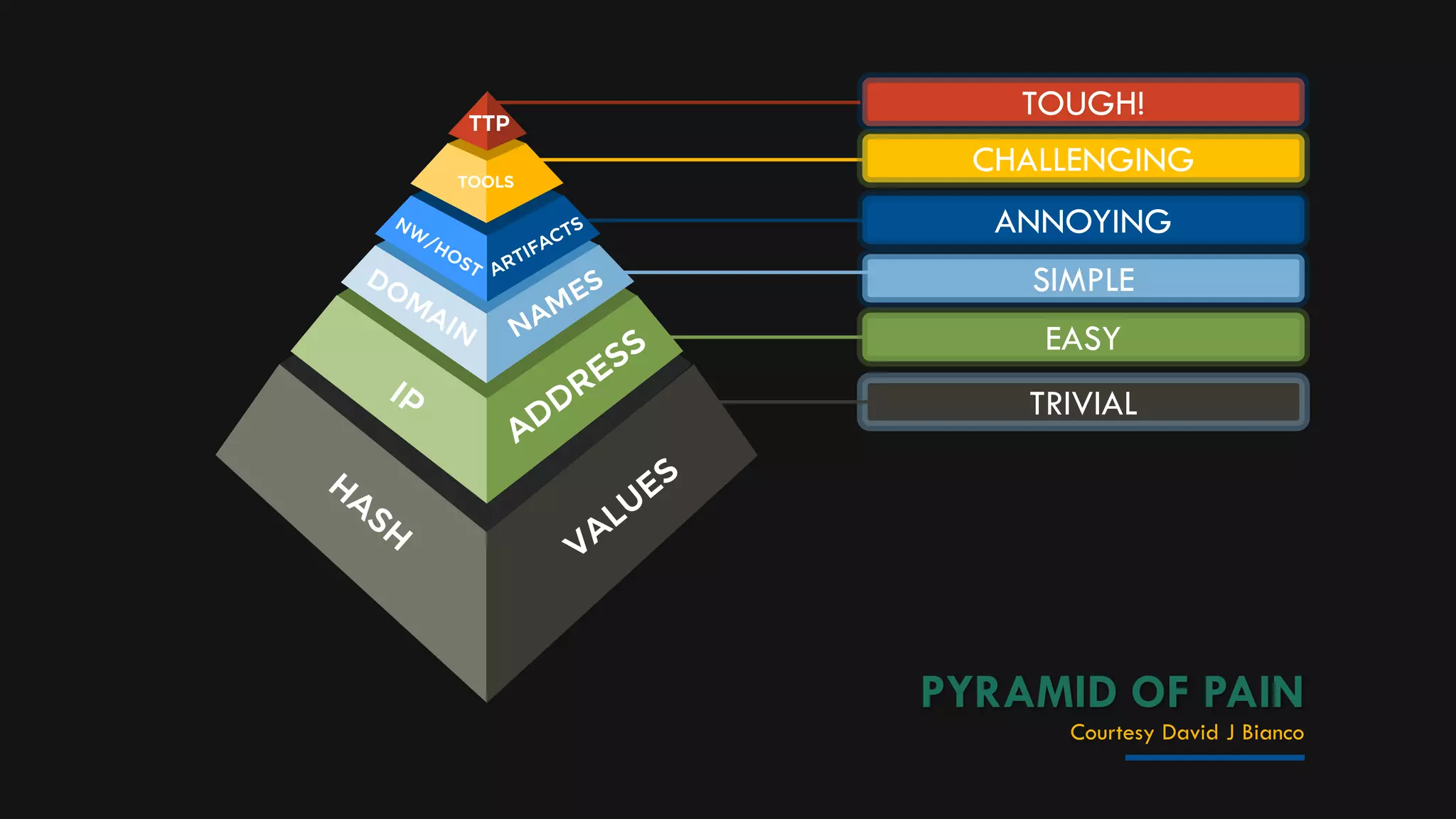
The Pyramid of Pain is a hierarchal model that categorizes defensive measures based on the point of difficulty and pain they get to attackers. The pyramid is divided into several layers, each represent a different type of justificatory action. The layers, from bottom to top, are as follows:
- Indicators of Compromise (IoCs): These are the most basic and easily obtainable pieces of information, such as IP addresses, domain names, and file hashes. While utilitarian for initial espial, they are also the easiest for attackers to modify.
- Tools: This layer involves identifying and blocking the tools used by attackers, such as malware, exploits, and hacking tools. Blocking these tools can disrupt an attacker's operations but requires more effort than merely blocking IoCs.
- Tactics, Techniques, and Procedures (TTPs): This layer focuses on realize and disrupting the specific methods and strategies used by attackers. By identifying and mitigate TTPs, defenders can make it much harder for attackers to run efficaciously.
- Infrastructure: This stratum involves name and interrupt the base used by attackers, such as command and control (C C) servers. Disrupting this infrastructure can significantly impede an attacker's ability to control compromised systems.
- Malware Configuration: This layer focuses on the specific configurations and settings used by malware. By interpret and disrupting these configurations, defenders can create it more difficult for malware to function as intended.
- Malware Code: This level involves canvas and disrupting the literal code of malware. By understanding the code, defenders can develop more effective countermeasures and make it much harder for attackers to use the same malware in the future.
- Attacker Identity: The top layer of the pyramid involves name and disrupting the individuals or groups behind the attacks. This is the most gainsay and impactful layer, as it immediately targets the source of the threat.
Implementing the Pyramid of Pain
To effectively enforce the Pyramid of Pain, organizations ask to adopt a multi layer approach to cybersecurity. This involves not only deploying technological controls but also fostering a culture of security sentience and uninterrupted improvement. Here are some steps to get get:
Assess Your Current Security Posture
Before enforce any new justificatory measures, it's crucial to assess your current security position. This involves identifying your assets, translate your threat landscape, and evaluating your existing defenses. Conducting a thorough risk assessment can aid you prioritize your efforts and allocate resources more effectively.
Develop a Comprehensive Security Strategy
Based on your risk assessment, evolve a comprehensive security strategy that aligns with the Pyramid of Pain. This scheme should include:
- Defensive Measures: Identify and enforce justificatory measures at each stratum of the pyramid, from IoCs to assailant individuality.
- Incident Response Plan: Develop an incidental response plan that outlines the steps to lead in the event of a security breach. This plan should include procedures for detecting, responding to, and recover from attacks.
- Continuous Monitoring: Implement continuous supervise to detect and respond to threats in existent time. This involves deploying security information and event management (SIEM) systems, intrusion catching systems (IDS), and other monitor tools.
- Security Awareness Training: Provide regular protection cognisance train to employees to help them recognize and respond to potential threats. This training should continue topics such as phishing, social engineering, and password protection.
Leverage Threat Intelligence
Threat intelligence plays a important role in implementing the Pyramid of Pain. By assemble and examine threat intelligence, organizations can gain insights into the tactics, techniques, and procedures used by attackers. This information can be used to acquire more effective justificatory measures and prioritize efforts found on the most relevant threats.
There are several sources of threat intelligence, including:
- Open Source Intelligence (OSINT): Information gathered from publicly uncommitted sources, such as societal media, forums, and blogs.
- Commercial Threat Intelligence: Information render by commercial vendors, such as threat intelligence feeds and reports.
- Industry Sharing: Information shared within industry groups and communities, such as Information Sharing and Analysis Centers (ISACs).
To efficaciously leverage threat intelligence, organizations should:
- Integrate Threat Intelligence: Integrate threat intelligence into survive protection tools and processes, such as SIEM systems and firewalls.
- Analyze Threat Intelligence: Analyze threat intelligence to name trends, patterns, and emerging threats. This analysis can aid prioritise defensive measures and allocate resources more effectively.
- Share Threat Intelligence: Share threat intelligence with industry peers and partners to enhance collective defense and improve overall security posture.
Implement Advanced Threat Detection
Advanced threat detection involves deploying technologies and techniques that can identify and respond to pervert attacks. This includes:
- Machine Learning and AI: Use machine acquire and hokey intelligence to detect anomalies and identify potential threats. These technologies can analyze tumid volumes of information and name patterns that may indicate malicious activity.
- Behavioral Analysis: Implement behavioural analysis to admonisher exploiter and scheme conduct for signs of compromise. This involves establishing baselines for normal behavior and find deviations that may signal an attack.
- Endpoint Detection and Response (EDR): Deploy EDR solutions to monitor and respond to threats at the endpoint level. EDR solutions can detect and respond to threats in existent time, providing a more proactive defense.
Conduct Regular Security Audits and Penetration Testing
Regular security audits and insight testing are essential for identify vulnerabilities and assessing the potency of defensive measures. These activities should be acquit by outside experts to ensure an unbiased assessment. The findings from these audits and tests can be used to refine and improve protection strategies.
When direct protection audits and penetration essay, organizations should:
- Identify Vulnerabilities: Identify vulnerabilities in systems, applications, and networks that could be overwork by attackers.
- Assess Risk: Assess the risk connect with name vulnerabilities and prioritize remediation efforts ground on the grade of risk.
- Implement Remediation: Implement remedy measures to address identify vulnerabilities and raise overall security position.
Foster a Culture of Security
Fostering a culture of security is all-important for the long term success of any cybersecurity scheme. This involves:
- Leadership Commitment: Ensuring that leadership is committed to cybersecurity and provides the necessary resources and support.
- Employee Engagement: Engaging employees in security initiatives and promote them to take an active role in protecting the organization.
- Continuous Improvement: Continuously amend protection practices and processes base on feedback, lessons learned, and issue threats.
Case Study: Applying the Pyramid of Pain
To illustrate the application of the Pyramid of Pain, consider a conjectural scenario where an brass is targeted by a convolute cyber attack. The attack involves the use of malware to exfiltrate sensible information. Here s how the organization can employ the Pyramid of Pain to mitigate the threat:
1. Indicators of Compromise (IoCs): The establishment detects strange network traffic and identifies specific IP addresses and domain names associated with the attack. These IoCs are blockade to prevent further communication with the attacker's infrastructure.
2. Tools: The organization identifies the specific malware used in the attack and blocks it from fulfill on its systems. This involves update antivirus signatures and deploy endpoint security solutions.
3. Tactics, Techniques, and Procedures (TTPs): The arrangement analyzes the attack to read the tactics, techniques, and procedures used by the aggressor. This info is used to develop more effectual justificatory measures, such as meshing cleavage and access controls.
4. Infrastructure: The organization identifies and disrupts the command and control (C C) servers used by the attacker. This involves working with ISPs and law enforcement to lead down the base.
5. Malware Configuration: The organization analyzes the malware conformation to understand how it operates and what datum it targets. This info is used to acquire more efficient countermeasures, such as behavioral analysis and anomaly detection.
6. Malware Code: The governance conducts a detailed analysis of the malware code to interpret its functionality and identify potential vulnerabilities. This info is used to develop patches and updates to protect against similar threats in the future.
7. Attacker Identity: The organization works with law enforcement and cybersecurity experts to identify the individuals or groups behind the attack. This info is used to build a case against the attackers and disrupt their operations.
By utilize the Pyramid of Pain, the organization can efficaciously extenuate the threat and enhance its overall protection posture. This multi layer approach ensures that defenders are targeting the most impactful areas and making it more difficult for attackers to achieve their goals.
Note: The Pyramid of Pain is a active model that requires continuous adaptation and improvement. Organizations should regularly review and update their defensive strategies to address egress threats and acquire attacker tactics.
In the realm of cybersecurity, the Pyramid of Pain provides a structured and effective framework for prioritizing defensive measures. By focus on the most impactful areas, organizations can raise their protection posture and create it more difficult for attackers to accomplish their goals. This multi layered approach ensures that defenders are place the most critical aspects of an attack, from indicators of compromise to attacker individuality. By implementing the Pyramid of Pain, organizations can establish a rich and springy defense against cyber threats, protect their assets and maintain the trust of their stakeholders.
Related Terms:
- pyramid of pain mitre
- pyramid of pain cti
- pyramid of pain image
- pyramid of pain ttp
- thm pyramid of pain walkthrough
- pyramid of pain security